Accelerate Data Initiatives
At the heart of Karlsgate's transformative strategy lies a commitment to simplification, automation, unparalleled adaptability, and a privacy-by-design approach.
Enter a New Era of Seamless Data Management
Addressing data complexity is often a manual and labor-intensive endeavor. The time and cost involved in managing data initiatives are substantial roadblocks. When the custom efforts for each integration are multiplied by the various data partners that organizations maintain, the total workload on IT balloons to uncontrollable levels. Compliance and standardization also suffer when the patchwork of custom data automation is left as technical debt.
The Karlsgate Identity Exchange (KIE) brings you advanced, consistent, and intelligent data handling along with seamless workflow automation. Experience the power to supercharge your AI data efforts with unparalleled precision and speed. Our solution is designed to make your journey smoother, providing you with the confidence to achieve exceptional results efficiently.
Automations
- Triggered routines
- Custom workflows
- Data format detection
- Semantic detection
- Data normalization
- Composite key creation
- Advanced cryptography
- Actionable De-identification
No-Code User Interface Features
- Perform an Overlap Analysis: compare two data sets to determine the overlap without ever sharing any information about their identifiable information
- Share Data Attributes: share data attributes for individuals in common on both files without ever disclosing any personal information about the individuals in their respective files, ensuring a secure and confidential exchange of valuable data insights
- Create an Anonymous Analytics File: create a complete anonymized and randomly sorted file made up of the overlapped records as well as attributes from either file on those records
- Create a Linkage Key: leverage this feature for uses cases such as "right to be forgotten" compliance or future linking/sharing of information without sending out a copy of your identifiable information
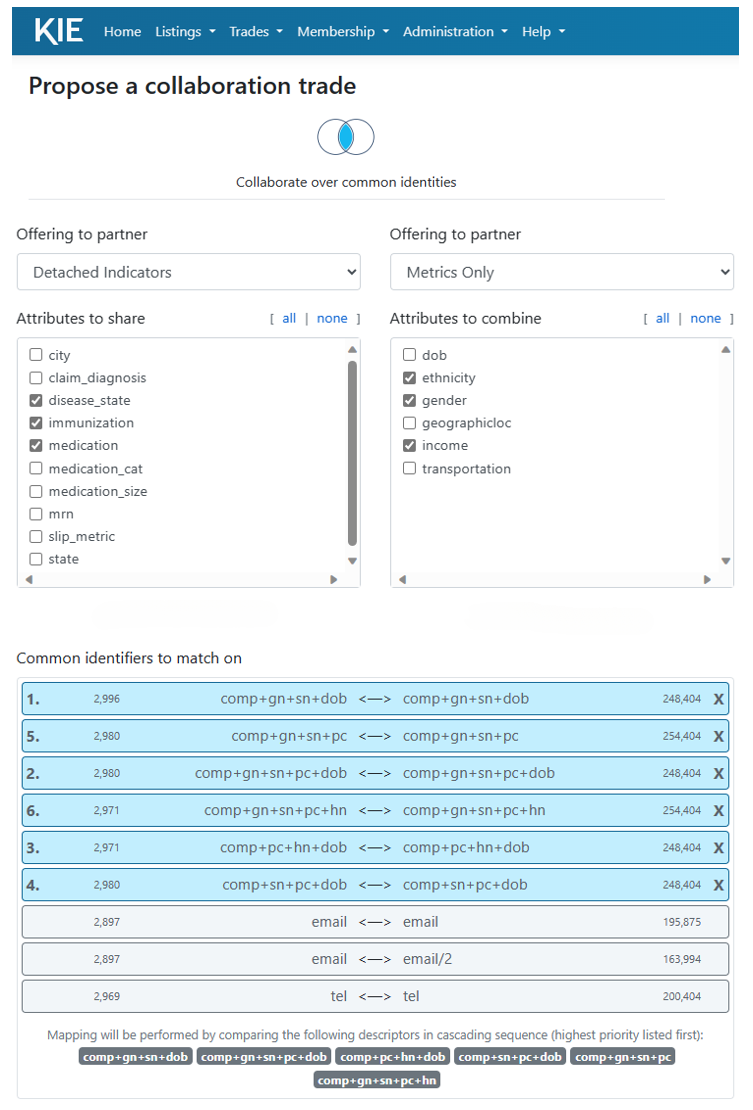
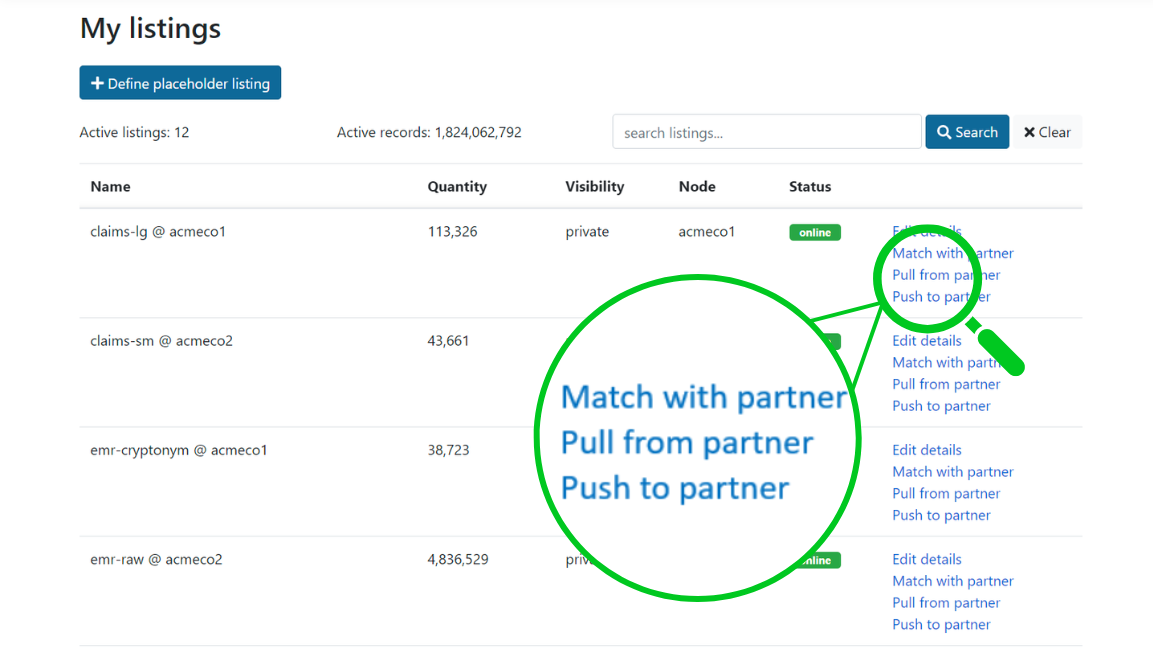
- Pull De-Identified Data: Receive actionably de-identified data from any number of data sources/partners and integrate into a single, de-duped file without receiving any PII or persistent IDs. All de-identified data is also randomly sorted to eliminate re-identification risks
- Push De-Identified Data: Send de-identified data to data partners without sharing any PII or persistent IDs. All de-identified data is also randomly sorted to eliminate re-identification risks
- Update De-Identified Data: Send and receive updates and integrate seamlessly without receiving any PII or persistent IDs
“Veritas was founded to make critical reference information accessible. Karlsgate enables us to do so outside the boundaries of traditional closed data ecosystems, all without interruption to current processes. This next-gen technology enables organizations across the healthcare continuum to seamlessly and compliantly improve data management and support better decision-making.”
Tom Dukes
Founding CEO
Veritas Data Research

“We see customers demanding better protection, easier delivery mechanisms, and more robust Health Equity data for comprehensive care. Our partnership with Karlsgate addresses these needs by offering a secure, scalable, and privacy-enhancing Health Equity solution that aligns with the evolving demands of the healthcare industry.”
Prashanth Sarpamale
CEO
Althea.ai

Understanding the Root of Today's Data Privacy Challenges
Explore how to solve the challenge of respecting privacy while retaining the benefits of a data-driven world with Karlsgate's solutions.

Unlocking the Power of Data Through Privacy Enhancing Technologies
Empower your organization with Privacy Enhancing Technologies. Secure data, enhance privacy, and drive growth across a wide range of indust...

Protecting Sensitive Data Without Sacrificing Utility: The Karlsgate Approach
Learn about Karlsgate's innovative solution for de-identifying sensitive data, ensuring compliance, security, and utility in today's data-d...


